Bonus: Distinction between vulnerabilities found by safety researchers and nil day updates in safety bulletins
I’m speculated to be preparing for an Azure class, however this PSA is just too necessary to attend. Because of some trolls I assumed it was price a couple of minutes to jot down this up. I blame an outdated model of Chrome that isn’t highlighting typos for any misspellings. j.ok.
At any time when I get trolled on one thing and it appears persons are making an attempt a bit too exhausting it at all times makes me marvel about their intentions. Typically they sound indignant as a substitute of merely declaring a mistake or expressing a distinct opinion. They normally aren’t following me. They typically have only a few followers (however not at all times). That occurred to me yesterday. The troll remark additionally obtained reposted by a non-cyber bot-looking account which made me additional suspicious. In the meantime, the tweet was getting likes by credible safety researchers.
As a aspect word, one other matter I get trolled exhausting on is IPv6. In the event you select to make use of it, ensure you perceive the small print of the protocol, how it's totally different from IP4v, and methods to configure it correctly to not expose inside system data. I typically marvel what the goals are of the IPv6 trolls and why they care a lot what model of IP I am operating on my *residence* community. Why does that matter to anybody else? Think about troll motivations.
I’m going to clarify methods to test your Chrome model as a result of having auto-update on doesn’t at all times work and in my case, I double checked and considered one of my techniques was not updated. I’ll additionally clarify methods to manually replace when auto-updates should not working. First, and clarification of several types of updates and why some are extra vital than others.
Several types of vulnerabilities and updates
For my new Twitter “good friend,” right here’s the distinction between this safety replace and a few others. Typically safety researchers will attempt to discover safety issues with Google. They’ll report them to Google and receives a commission for them. In principle, the one folks that learn about that replace are the safety researcher and Google.
On this case, Google is reporting that somebody is actively exploiting a safety downside within the wild, for which no replace beforehand existed. That’s referred to as a Zero Day, which means a repair for the issue has been out there for zero days. Attackers are utilizing it to use techniques and there’s nothing you are able to do about it (besides probably community safety which I write lots about on my weblog and have extra coming!)
In current bulletins, Google acknowledged that attackers had been exploiting safety vulnerabilities which signifies that the vulnerabilities obtained found when attackers exploited a system — not as a result of a safety researcher shared a vulnerability with Google.
Who’re these attackers exploiting Google browsers? Nicely we’ve lots happening on the earth proper now as I’ve defined earlier than and everybody needs to be on excessive alert. It seems that a number of international locations could also be coordinating on cyber assaults from studies I’ve learn. Regardless of the case, it’s a good suggestion to verify your techniques are at all times updated.
I retweeted a information article a few Google replace that was being exploited within the wild. The replace is coming in a few days, however you may get it manually.
Test your Google Chrome Model
I went in and checked my Google Chrome model and counsel you do as effectively. Right here’s the place you test on a Mac — Click on on Chrome within the prime menu and About Google Chrome. Edit: I simply checked on my Home windows machine. Kind “Replace Chrome” within the search bar and click on the button. On telephones you’ll be able to test your purposes for updates. It’s humorous that my important different does that in all probability extra typically than I do. On daily basis he asks me, what number of updates do you suppose I’ve at present?
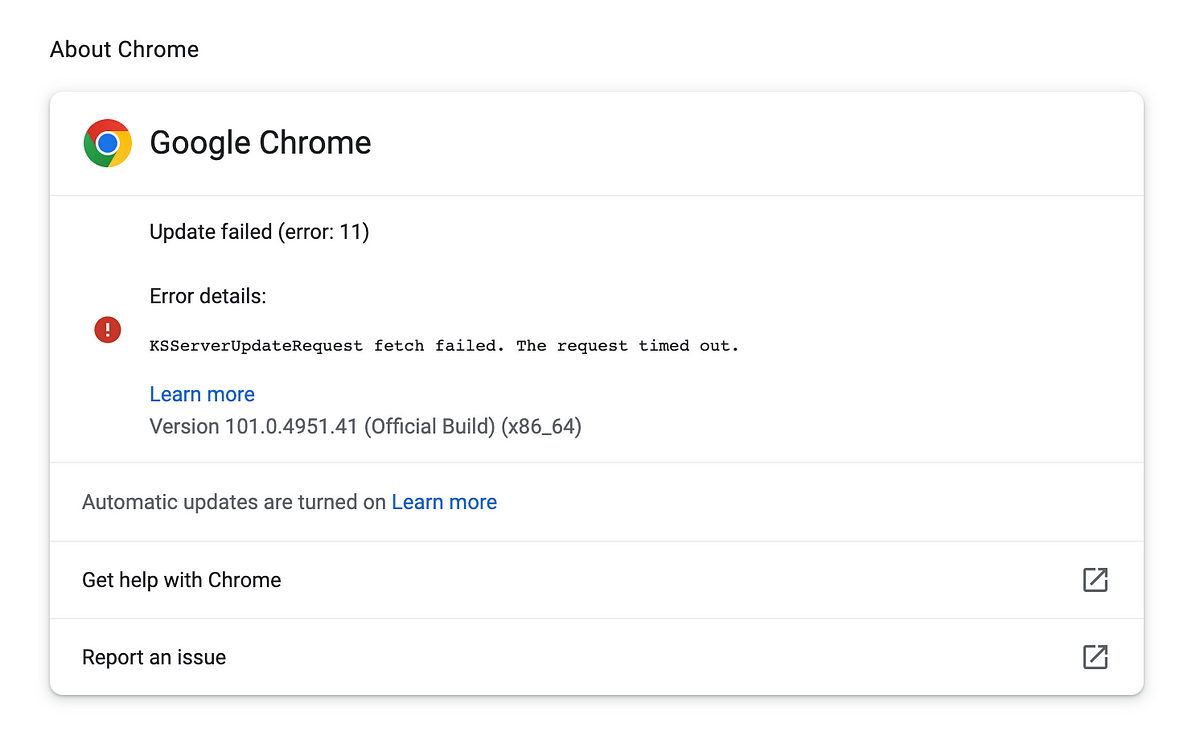
As soon as once more my updates should not working. I used to be unsure if I used to be operating the newest model as a result of the Google releases web page has the newest “beta” model. However I assume every thing is in everlasting beta at Google.
After I manually up to date I obtained this model: 101.0.4951.41
New: On the identical day I up to date one other Mac and obtained this model:Model 101.0.4951.54 (Official Construct) (x86_64)
I searched on that model to search out the newest Google steady launch model which oddly doesn’t come up once I seek for “newest Google model” in Google:
Moreover, once I search on Google Steady Model I get previous cached outcomes.

Manually replace Google Chrome
Google replace wasn’t working for me. I obtained this error:

I presume that is my fault as a result of in the event you learn my blogs I’m not the typical Web consumer. Nonetheless, I’ve the community open to the Google replace servers. I actually hope that Google is NOT requiring third-party cookies or inbound community visitors for this to work.
Earlier than you replace you may need to change your DNS servers to this service from CloudFlare which blocks identified malicious domains:
To replace manually go to the Google obtain web page, manually obtain Google Chrome, and reinstall it. Listed here are some issues you may need:
Can’t obtain utilizing Google Chrome (particularly whether it is contaminated)
Obtain from an alternate browser reminiscent of Safari or a Microsoft browser. The final time I did this I utterly deleted Google Chrome from my system and reinstalled.
Ensure you shut down Google chrome.
You may’t set up a brand new model of Google Chrome when you’ve gotten Google Chrome operating. Terminate it after which set up the brand new model.
Change the prevailing model.
You need to be sure the previous model is eliminated so that you don’t by chance run it. As I simply talked about, I utterly deleted Google Chrome earlier than putting in the brand new model final time. Whenever you set up on a Mac select the choice to “change” as a substitute of conserving each variations round. I haven’t examined on Home windows however in the event you get an identical possibility do the identical there.
That’s it for now — again to work!
Teri Radichel — Comply with me @teriradichel
© 2nd Sight Lab 2022
____________________________________________

Need to be taught extra about Cybersecurity and Cloud Safety? Take a look at: Cybersecurity for Executives within the Age of Cloud on Amazon
Want Cloud Safety Coaching? 2nd Sight Lab Cloud Safety Coaching
Is your cloud safe? Rent 2nd Sight Lab for a penetration take a look at or safety evaluation.
Have a Cybersecurity or Cloud Safety Query? Ask Teri Radichel by scheduling a name with IANS Analysis.
Cybersecurity & Cloud Safety Assets by Teri Radichel: Cybersecurity and Cloud safety courses, articles, white papers, displays, and podcasts