A brand new Golang-based botnet dubbed HinataBot has been noticed to leverage recognized flaws to compromise routers and servers and use them to stage distributed denial-of-service (DDoS) assaults.
“The malware binaries seem to have been named by the malware creator after a personality from the favored anime sequence, Naruto, with file identify constructions comparable to ‘Hinata-<OS>-<Structure>,'” Akamai stated in a technical report.
Among the many strategies used to distribute the malware are the exploitation of uncovered Hadoop YARN servers and safety flaws in Realtek SDK units (CVE-2014-8361), Huawei HG532 routers (CVE-2017-17215, CVSS rating: 8.8).
Unpatched vulnerabilities and weak credentials have been a low-hanging fruit for attackers, representing a straightforward, well-documented entry level that doesn’t require subtle social engineering ways or different strategies.
The risk actors behind HinataBot are stated to have been lively since at the very least December 2022, with the assaults first trying to make use of a generic Go-based Mirai variant earlier than switching to their very own customized malware ranging from January 11, 2023.
Since then, newer artifacts have been detected in Akamai’s HTTP and SSH honeypots as lately as this month, packing in additional modular performance and added safety measures to withstand evaluation. This means that HinataBot continues to be in lively improvement and evolving.
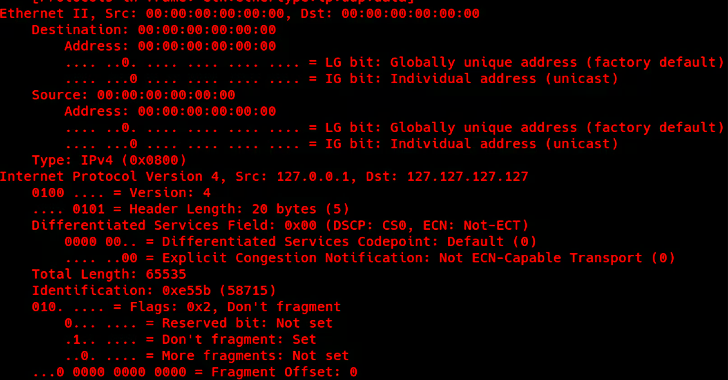
The malware, like different DDoS botnets of its variety, is able to contacting a command-and-control (C2) server to hear for incoming directions and provoke assaults in opposition to a goal IP deal with for a specified length.
Whereas early variations of the botnet utilized protocols comparable to HTTP, UDP, TCP, and ICMP to hold out DDoS assaults, the newest iteration is restricted to only HTTP and UDP. It is not instantly recognized why the opposite two protocols have been axed.
Akamai, which performed 10-second assault checks utilizing HTTP and UDP, revealed that the HTTP flood generated 3.4 MB of packet seize information and pushed 20,430 HTTP requests. The UDP flood, however, created 6,733 packets for a complete of 421 MB of packet seize information.
In a hypothetical real-world assault with 10,000 bots, a UDP flood would peak at greater than 3.3 terabit per second (Tbps), leading to a potent volumetric assault. An HTTP flood would generate a visitors of roughly 27 gigabit per second (Gbps)
The event makes it the newest to hitch the ever-growing record of rising Go-based threats comparable to GoBruteforcer and KmsdBot.
“Go has been leveraged by attackers to reap the advantages of its excessive efficiency, ease of multi-threading, its a number of structure and working system cross-compilation help, but additionally doubtless as a result of it provides complexity when compiled, rising the issue of reverse engineering the ensuing binaries,” Akamai stated.
Uncover the Hidden Risks of Third-Get together SaaS Apps
Are you conscious of the dangers related to third-party app entry to your organization’s SaaS apps? Be part of our webinar to be taught concerning the varieties of permissions being granted and how you can decrease danger.
The findings additionally come as Microsoft revealed that TCP assaults emerged as probably the most frequent type of DDoS assault encountered in 2022, accounting for 63% of all assault visitors, adopted by UDP floods and amplification assaults (22%), and packet anomaly assaults (15%).
Moreover getting used as distractions to hide extortion and information theft, DDoS assaults are additionally anticipated to rise as a result of arrival of recent malware strains which can be able to concentrating on IoT units and taking up accounts to realize unauthorized entry to assets.
“With DDoS assaults changing into extra frequent, subtle, and cheap to launch, it is vital for organizations of all sizes to be proactive, keep protected all yr spherical, and develop a DDoS response technique,” the tech big’s Azure Community Safety Crew stated.