The zero-day exploitation of a now-patched medium-severity safety flaw within the Fortinet FortiOS working system has been linked to a suspected Chinese language hacking group.
Menace intelligence agency Mandiant, which made the attribution, mentioned the exercise cluster is a part of a broader marketing campaign designed to deploy backdoors onto Fortinet and VMware options and preserve persistent entry to sufferer environments.
The Google-owned risk intelligence and incident response agency is monitoring the malicious operation underneath its uncategorized moniker UNC3886, a China-nexus risk actor.
“UNC3886 is a complicated cyber espionage group with distinctive capabilities in how they function on-network in addition to the instruments they make the most of of their campaigns,” Mandiant researchers mentioned in a technical evaluation.
“UNC3886 has been noticed concentrating on firewall and virtualization applied sciences which lack EDR help. Their means to govern firewall firmware and exploit a zero-day signifies they’ve curated a deeper-level of understanding of such applied sciences.”
It is value noting that the adversary was beforehand tied to a different intrusion set concentrating on VMware ESXi and Linux vCenter servers as a part of a hyperjacking marketing campaign designed to drop backdoors resembling VIRTUALPITA and VIRTUALPIE.
The most recent disclosure from Mandiant comes as Fortinet revealed that authorities entities and enormous organizations had been victimized by an unidentified risk actor by leveraging a zero-day bug in Fortinet FortiOS software program to lead to information loss and OS and file corruption.
The vulnerability, tracked as CVE-2022-41328 (CVSS rating: 6.5), considerations a path traversal bug in FortiOS that would result in arbitrary code execution. It was patched by Fortinet on March 7, 2023.
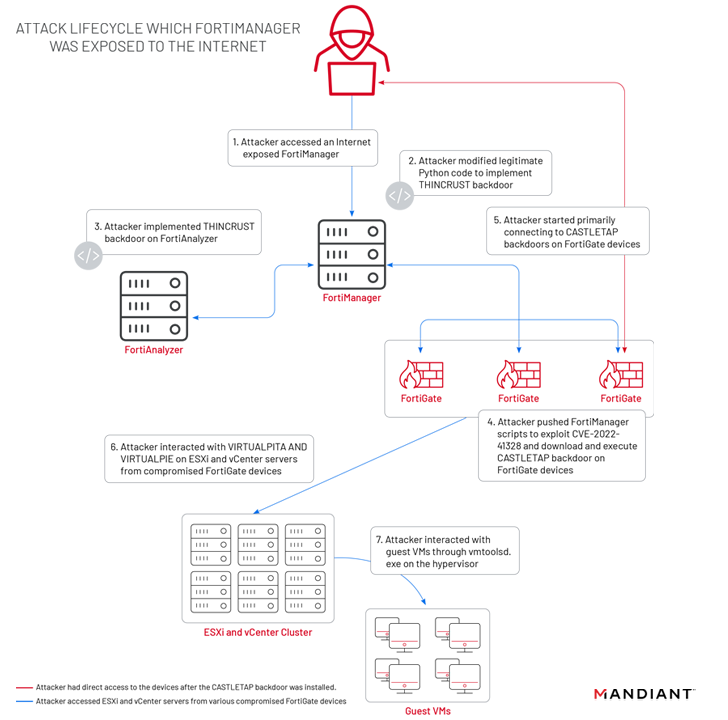
In accordance with Mandiant, the assaults mounted by UNC3886 focused Fortinet’s FortiGate, FortiManager, and FortiAnalyzer home equipment to deploy two totally different implants resembling THINCRUST and CASTLETAP. This, in flip, was made attainable owing to the truth that the FortiManager machine was uncovered to the web.
THINCRUST is a Python backdoor able to executing arbitrary instructions in addition to studying and writing from and to information on disk.
The persistence afforded by THINCRUST is subsequently leveraged to ship FortiManager scripts that weaponize the FortiOS path traversal flaw to overwrite reputable information and modify firmware photos.
This features a newly added payload referred to as “/bin/fgfm” (known as CASTLETAP) that beacons out to an actor-controlled server in order to simply accept incoming directions that enable it to run instructions, fetch payloads, and exfiltrate information from the compromised host.
“As soon as CASTLETAP was deployed to the FortiGate firewalls, the risk actor linked to ESXi and vCenter machines,” the researchers defined. “The risk actor deployed VIRTUALPITA and VIRTUALPIE to determine persistence, permitting for continued entry to the hypervisors and the visitor machines.”
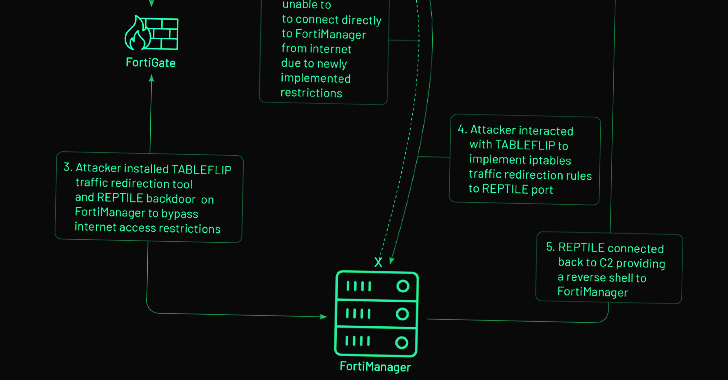
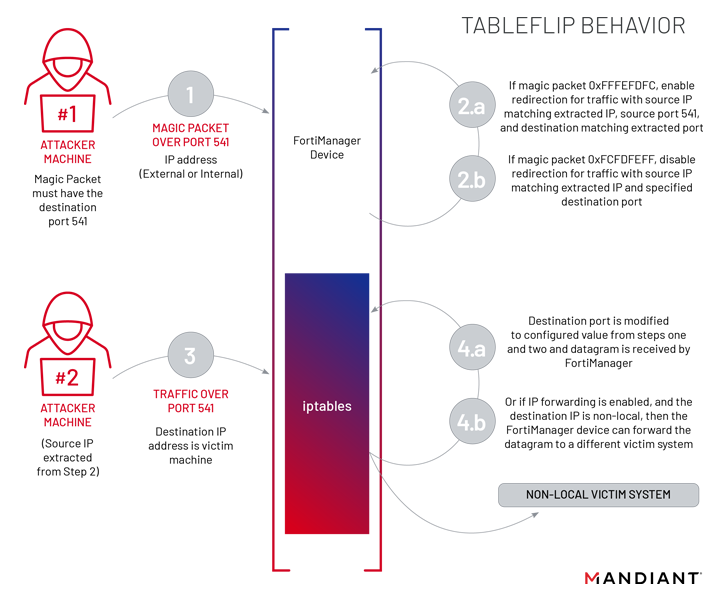
Alternatively, on FortiManager units that implement web entry restrictions, the risk actor is claimed to have pivoted from a FortiGate firewall compromised with CASTLETAP to drop a reverse shell backdoor named REPTILE (“/bin/klogd”) on the community administration system to regain entry.
Uncover the Hidden Risks of Third-Get together SaaS Apps
Are you conscious of the dangers related to third-party app entry to your organization’s SaaS apps? Be part of our webinar to study concerning the sorts of permissions being granted and decrease threat.
Additionally employed by UNC3886 at this stage is a utility dubbed TABLEFLIP, a community visitors redirection software program to attach on to the FortiManager machine whatever the access-control listing (ACL) guidelines put in place.
That is removed from the primary time Chinese language adversarial collectives have focused networking tools to distribute bespoke malware, with current assaults making the most of different vulnerabilities in Fortinet and SonicWall units.
The revelation additionally comes as risk actors are creating and deploying exploits quicker than ever earlier than, with as many as 28 vulnerabilities exploited inside seven days of public disclosure — a 12% rise over 2021 and an 87% rise over 2020, based on Rapid7.
That is additionally vital, not least as a result of China-aligned hacking crews have change into “significantly proficient” at exploiting zero-day vulnerabilities and deploying customized malware to steal consumer credentials and preserve long-term entry to focus on networks.
“The exercise […] is additional proof that superior cyber espionage risk actors are making the most of any expertise obtainable to persist and traverse a goal setting, particularly these applied sciences that don’t help EDR options,” Mandiant mentioned.